What is Threat Modeling?
Imagine you have a fantastic online toy store, full of cool gadgets and games. You want everyone to visit and feel safe shopping there, right? Threat modeling is like drawing a map of your store and thinking about all the ways something bad could happen – not just to your toys, but to your customers’ information too. It’s a smart way to find problems before they actually become problems, helping you protect your business and keep your shoppers happy and secure.
What’s the Big Idea Behind Threat Modeling?
Threat modeling is all about being a security detective for your online business. Instead of waiting for something bad to happen, you actively try to figure out what could go wrong. Think of it like this: if you were building a treehouse, you wouldn’t just nail some boards together and hope it’s strong. You’d think, “What if a big gust of wind comes? What if too many friends climb in at once? How can I make it super sturdy and safe?”
That’s what threat modeling does for your online store. You look at your website, how it works, what information it holds, and then you imagine all the sneaky ways someone might try to cause trouble. Maybe they try to steal customer names, mess with prices, or even make your website stop working. By thinking like a “bad guy” first, you can put up strong defenses and keep everything running smoothly. It’s a proactive approach, meaning you’re preventing issues before they start, rather than just reacting to them later. For an online store, this is super important because it helps protect sensitive customer details and ensures a smooth shopping experience.
Why Do Online Stores Need Threat Modeling?
Online stores, also known as e-commerce businesses, are busy places. They handle lots of important stuff: customer names, addresses, payment information, and product details. Just like a physical store needs locks on its doors and security cameras, an online store needs digital protection. Without proper security, an online store faces several risks:
- Data Breaches: This is when unauthorized people get access to private customer information, like credit card numbers or home addresses. It’s a huge problem that can make customers lose trust.
- Fraud: Someone might try to make fake purchases using stolen credit cards, which can cost the business money and time.
- Website Downtime: Attacks can sometimes make a website crash or become very slow, meaning customers can’t shop, and the business loses sales.
- Reputation Damage: If an online store isn’t secure, news travels fast. Customers might decide to shop elsewhere, and it can be hard to earn back their trust.
All these risks highlight why threat modeling isn’t just a good idea; it’s a necessity. When customers feel safe and confident that their information is protected, they are much more likely to shop with you again and tell their friends about your store. This feeling of security builds strong customer relationships, much like how collecting and displaying authentic customer reviews helps build trust in your products and services. A secure platform shows customers you care about their safety, making them feel valued and secure in their shopping journey.
The Steps to Becoming a “Security Detective”
Becoming a security detective for your online store isn’t overly complicated, especially when you break it down into a few clear steps. It’s like solving a puzzle, piece by piece.
Step 1: What Are We Protecting? (Defining the System)
First things first, you need to know exactly what you’re trying to keep safe. For an online store, this means thinking about all the valuable “stuff” you have. This includes:
- Customer Data: Things like names, email addresses, shipping addresses, and, most importantly, payment information. This is very private!
- Website Functionality: Making sure your checkout process works, product pages display correctly, and customers can log into their accounts.
- Product Information: Keeping your product descriptions, prices, and stock levels accurate and safe from being changed by outsiders.
- Your Online Store Platform: Understanding how your website is built, what systems it uses, and how different parts talk to each other.
Imagine drawing a simple map of your online store. Where does customer information go when someone makes a purchase? Where is it stored? Knowing this helps you understand the “treasure” you need to guard.
Step 2: What Can Go Wrong? (Identifying Threats)
Once you know what you’re protecting, the next step is to imagine all the possible bad things that could happen. This is where you put on your “bad guy” hat (but only for good!). You brainstorm different types of attacks or problems.
Think about common ways trouble could start:
- Someone trying to trick a customer into giving away their password.
- Someone trying to change the price of an item on your website without permission.
- A bad actor trying to make your website slow or completely unavailable.
- Accidental mistakes, like a glitch that exposes some private information.
This step is about being imaginative but also realistic. You list all the potential threats, big and small, that could impact your online store and its customers.
Step 3: What Are We Going to Do About It? (Mitigating Threats)
After you’ve identified all the potential problems, it’s time to figure out solutions. These solutions are called “mitigations,” and they’re like putting up security fences, installing strong locks, or adding alarms to your home.
For an online store, mitigations could include:
- Strong Passwords: Making sure customers and staff use complex passwords and encouraging them to change them often.
- Encryption: Scrambling sensitive data (like credit card numbers) so that even if someone gets it, they can’t read it.
- Secure Payment Gateways: Using trusted services to handle credit card transactions, so your store never directly stores sensitive payment details.
- Regular Updates: Keeping all your website software and tools updated, as updates often include new security patches.
- Access Controls: Making sure only the right people can access certain parts of your website’s backend or customer data.
The goal here is to come up with practical ways to reduce the chances of a threat actually happening or to lessen the damage if it does. A smooth and secure transaction process directly contributes to a great customer retention strategy, as happy and safe customers are loyal customers.
Step 4: Did It Work? (Verifying and Improving)
The final step is to check if your security measures are actually working. You wouldn’t just install a lock and never try the key, right? Security isn’t a one-time thing; it’s an ongoing process.
This step involves:
- Testing Your Defenses: Regularly checking your website for weaknesses, perhaps by hiring security experts to try and find holes.
- Monitoring: Keeping an eye on your website for any unusual activity that might signal an attack.
- Reviewing and Updating: As your online store grows and technology changes, new threats appear. You need to constantly review your threat model and update your defenses.
Just like businesses continually work to improve their customer experience based on feedback and new ideas, they must also continuously refine their security measures. This ensures your online store remains safe and trustworthy for everyone.
Popular Ways to Model Threats (Tools and Methods Made Simple)
There are different ways security experts approach threat modeling, but many of them share similar ideas. Here are a couple of popular methods explained in a simple way.
STRIDE: Thinking Like a Bad Guy (Simplified)
STRIDE is a helpful checklist that lets you think about different kinds of attacks. Each letter stands for a different type of threat:
- Spoofing: This is when someone pretends to be someone else.
- E-commerce Example: A hacker creates a fake login page that looks exactly like your store’s, trying to trick customers into giving away their passwords.
- Tampering: This means changing data without permission.
- E-commerce Example: Someone tries to illegally change the price of a product on your website to make it super cheap for themselves or others.
- Repudiation: This is when someone denies doing something, even though they did it.
- E-commerce Example: A fraudulent customer places an order but then denies they ever did, trying to get the product for free. Your system needs proof they made the order.
- Information Disclosure: This is about secrets getting out.
- E-commerce Example: A hacker manages to access your customer database and steals private details like credit card numbers or home addresses.
- Denial of Service (DoS): This means making a website or service unavailable to its real users.
- E-commerce Example: Attackers flood your website with so much fake traffic that it slows down or crashes, so real customers can’t make purchases.
- Elevation of Privilege: This is when someone gets more access than they should have.
- E-commerce Example: A regular customer somehow finds a way to get “admin” access to your website, letting them see or do things they shouldn’t.
By going through each STRIDE category, you can systematically think about what could go wrong in your online store.
DREAD: How Bad is It? (Simplified Risk Assessment)
Once you’ve found a bunch of potential threats using methods like STRIDE, the next question is: “Which ones should I fix first?” DREAD helps you prioritize by asking five simple questions about each threat:
- Damage: If this threat actually happened, how bad would it be? (From “a little inconvenient” to “completely catastrophic”).
- Reproducibility: How easy is it for someone to make this threat happen again and again? (From “very hard” to “super easy”).
- Exploitability: How hard or easy is it to actually launch this attack? Do you need special skills or tools, or is it simple? (From “needs a genius” to “anyone can do it”).
- Affected Users: How many people would be impacted if this threat happened? (From “just one person” to “all your customers”).
- Discoverability: How easy is it for a bad actor to find this weakness in the first place? (From “hidden very well” to “obvious to everyone”).
By answering these questions for each threat, you can give them a score and decide which ones are the most urgent to fix. This is similar to how e-commerce businesses prioritize efforts based on data, like improving a specific part of their site that has a low conversion rate. You focus on the biggest risks first to get the most protection for your effort.
Threat Modeling and Your Online Business
So, how does all this security detective work connect back to your online business and its success? It’s all about building trust and protecting your hard-earned reputation.
Building Customer Trust Through Security
Think about it: would you rather shop at a store that looks run-down and unsafe, or one that is clean, well-lit, and clearly takes care of its customers? The online world is no different. When customers know their personal information and payment details are safe with your store, they feel secure. This feeling of safety directly builds trust.
Trust is a huge deal in e-commerce. It encourages customers to make purchases, return to your store again and again, and even tell their friends and family about their positive experiences. This is the essence of word-of-mouth marketing – when customers become your best advocates because they had a great experience, part of which is feeling secure. A strong security posture, made possible through threat modeling, reinforces the positive image of your brand and makes customers confident in every interaction.
The Role of Reviews and Loyalty in a Secure Environment
Customer reviews aren’t just about what people think of a product; they also reflect their overall experience with your store. A positive review often means the customer had a smooth, easy, and, importantly, secure shopping journey. If customers don’t trust your site’s security, they are less likely to buy, and even less likely to leave a positive review or join a special program.
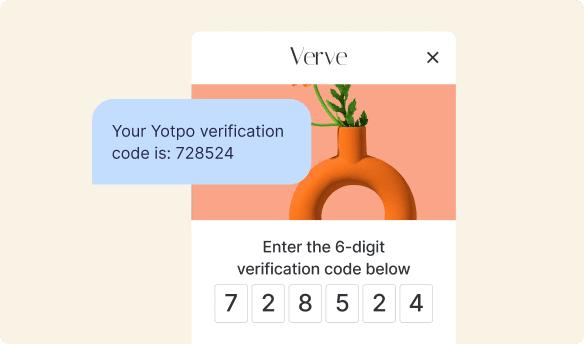
This is where tools like Yotpo Reviews and Yotpo Loyalty come in. Yotpo Reviews helps businesses collect and display authentic feedback from real customers. When a customer leaves a review, it shows they trust your brand enough to share their experience. A secure shopping environment encourages customers to confidently share their thoughts, knowing their interactions are protected.
Similarly, Yotpo Loyalty empowers businesses to create exciting reward programs for their customers. When customers enroll in a loyalty program, they are sharing more information and committing to a longer relationship with your brand. They will only do this if they feel safe and valued. A strong security foundation ensures that customer data for loyalty programs is protected, fostering a deeper, more trusting relationship. These tools work hand-in-hand with good security practices to create a comprehensive and positive customer experience, building a community of happy and loyal shoppers.
| Threat Category | Simple Example (E-commerce) | What Can Go Wrong? | Simple Solution |
|---|---|---|---|
| Data Theft | Someone steals customer credit card numbers or personal details. | Customers lose money, personal information, and completely lose trust in your store. | Encrypt all sensitive payment info, use secure, reputable payment gateways, and limit what data you store. |
| Website Downtime | Your website crashes or becomes very slow, so customers can’t browse or shop. | Lost sales, frustrated customers who will go elsewhere, and damage to your brand’s reputation. | Use reliable web hosting, have backup systems in place, and protect against “Denial of Service” attacks. |
| Fake Orders / Fraud | Someone uses stolen credit cards to make purchases from your store. | Your business loses money on the products shipped and potentially faces chargebacks. | Implement fraud detection tools, carefully review suspicious orders, and use address verification services. |
| Account Takeover | A hacker gains unauthorized access to a customer’s login account on your site. | Customer’s personal info might be stolen, or fake orders could be placed using their saved details. | Enforce strong password policies, offer two-factor authentication, and monitor for unusual login activity. |
| Product Price Tampering | Someone illegally changes a product’s price to be much lower than it should be. | Your business loses money on discounted sales, and it creates unfair advantages. | Implement strict access controls for content management, conduct regular data integrity checks, and use version control. |
Keeping Your Online Store Safe: A Continuous Journey
You know, keeping an online store safe isn’t something you do just once and then forget about. It’s more like taking care of a garden – you have to water it regularly, pull weeds, and make sure it stays healthy all year long. Security is a continuous journey. New technologies bring new ways for things to go wrong, so businesses must always be learning and adapting.
By regularly doing threat modeling, you ensure your online store stays protected against new and evolving dangers. This constant attention to security helps your business not just survive, but truly thrive. When customers feel secure, they’re more likely to shop confidently, leave positive reviews, and engage with your loyalty programs. This fosters long-term relationships and helps your business grow. Just as businesses constantly work to improve their ecommerce marketing funnel and customer satisfaction, they must also consistently work on their security. It’s a vital part of building a successful and lasting online presence.
So, what is threat modeling? It’s simply about being smart and proactive. It’s making a plan to protect your online store, your products, and most importantly, your amazing customers. By thinking like a security detective, you can build a safer, more trustworthy online shopping experience that encourages happy customers to return again and again. This careful planning and protection are fundamental to building a strong brand and supporting the success of any e-commerce business looking to grow with tools like Yotpo’s Reviews and Loyalty programs.

















 Join a free demo, personalized to fit your needs
Join a free demo, personalized to fit your needs