What is a Two-Factor Authentication? (2FA)
Imagine you have a super special treasure chest. You keep your favorite toys, drawings, and secrets inside. You wouldn’t want just anyone to open it, right? So, you put a lock on it. That’s like a password for your online accounts.
But what if someone sneaky finds your key? Or maybe they guess it? That’s where Two-Factor Authentication, or 2FA for short, comes in! Think of 2FA as adding a second, extra lock to your treasure chest. Now, even if someone finds the first key, they still can’t open it without the second one. This makes your online accounts much, much safer.
In this article, we’re going to explore what 2FA is, why it’s so important, and how it acts like a digital superhero protecting your online world. It’s a simple step that adds a huge layer of security to your digital life, making it harder for unauthorized people to get into your private stuff.
What is Authentication?
Before we dive deeper into 2FA, let’s quickly understand “authentication.” It’s a fancy word for proving who you are. When you log into a website or an app, the website needs to know it’s really you, and not someone pretending to be you. This is called authentication.
Most of the time, the first way you prove who you are is with a password. You enter your username and then your secret password. If they match, the website says, “Okay, come on in!” This is like showing your ID card to get into a special club. It’s the first step in making sure only you can access your accounts.
Why Do We Need More Than Just a Password?
Passwords are good, but they’re not perfect. Sometimes, passwords can be:
- Guessed: If your password is too simple (like “123456” or “password”), a computer can guess it very quickly.
- Stolen: Sometimes, sneaky people (called hackers) might try to trick you into giving away your password. Or, if a website you use has a security problem, your password could be exposed.
- Forgotten: We all forget things! And if you write your password down, someone might find it.
Because passwords aren’t always super strong on their own, we need something extra to protect our important online places, like our email, banking apps, or even our favorite shopping sites. Just like you might have a fence around your yard AND a lock on your door, we need more than one defense online.
Understanding Two-Factor Authentication (2FA)
So, what exactly is this “two-factor” magic? It means that to get into your account, you need to provide two different types of proof that you are who you say you are. These two proofs come from different “factors.” Think of it like this:
- Something you know: This is usually your password. It’s something only you should remember.
- Something you have: This is usually a physical item, like your smartphone, a special security key, or an app on your phone. It’s something only you should possess.
When you combine these two different types of proof, it becomes much, much harder for someone else to get into your account, even if they somehow got your password. They would also need to have your phone or your special key, which is very unlikely!
The Three Types of Authentication Factors
To make things even clearer, let’s look at the three main types of “factors” that can be used for authentication:
Something You Know
This is information that only you are supposed to know. It’s like a secret code in your brain.
- Passwords: The most common “something you know.” Make them long and tricky!
- PINs (Personal Identification Numbers): Like the four-digit code you use for your bank card.
- Security Questions: Sometimes a website asks “What was your first pet’s name?” or “What city were you born in?” But be careful, sometimes these can be guessed too.
Something You Have
This is a physical item that belongs to you and is usually with you. It’s like having a key in your pocket.
- Your Phone: This is the most common for 2FA. The website sends a special code to your phone as a text message.
- Authenticator Apps: These are special apps on your phone (like Google Authenticator or Authy) that create a new, temporary code every 30-60 seconds.
- Hardware Security Keys: These are small USB devices that you plug into your computer. They’re like a super-secure physical key for your online accounts.
Something You Are
This is something unique about your body. It’s like your unique fingerprints or your face.
- Fingerprint Scan: Many smartphones have this! You just touch your finger to a sensor.
- Face Scan (Face ID): Your phone might scan your face to unlock it or approve purchases.
- Retina or Iris Scan: Less common for everyday use, but some high-security systems might scan your eye.
When you use 2FA, you usually combine “something you know” (your password) with “something you have” (like a code sent to your phone) or “something you are” (like your fingerprint). This combination creates a much stronger barrier against unwanted visitors.
How Does Two-Factor Authentication Work?
Let’s walk through an example of how 2FA works when you try to log into an account:
- Step 1: You enter your password (Something You Know). You go to your favorite online store or social media site and type in your username and password, just like always. The website checks if it’s the correct password.
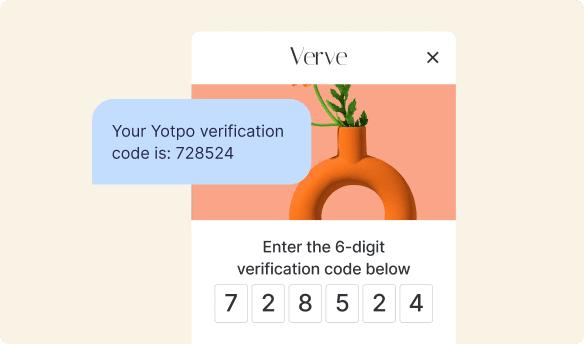
- Step 2: The website asks for a second code (Something You Have). Instead of letting you right in, the website says, “Hold on! We need one more thing to make sure it’s really you.” It then sends a unique, temporary code to your phone via a text message, or it asks for a code from your authenticator app.
- Step 3: You enter the second code. You quickly check your phone, find the code, and type it into the website.
- Step 4: You’re in! If both your password and the second code are correct, the website knows it’s truly you, and you get access to your account.
This whole process usually only takes a few extra seconds, but it adds a massive amount of security. It’s a small effort for a big safety reward.
Common Types of 2FA in Action
Here are some of the most common ways you’ll see 2FA used online:
SMS Codes (Text Messages)
This is probably the most common type. A website sends a short, temporary code to your registered phone number. You then type that code into the login screen. It’s super easy to use, but if someone steals your phone or can trick your phone company, it’s slightly less secure than other methods.
Authenticator Apps
Apps like Google Authenticator or Authy generate a new, time-sensitive code right on your phone every 30-60 seconds. These codes work even if you don’t have phone service, as long as your phone’s clock is correct. They are generally more secure than SMS codes because they don’t rely on your phone’s network provider.
Biometrics (Fingerprint or Face Scan)
On devices that support it, you might use your fingerprint or face to confirm your identity. This is incredibly convenient and often very secure because your body is unique to you. It’s like having your own built-in security key!
Hardware Security Keys
These are small physical devices, often looking like a USB stick. When you log in, you plug the key into your computer or tap it to your phone. They are considered one of the most secure forms of 2FA because they are very difficult to copy or fake. They are perfect for protecting your most important accounts.
Using any of these methods adds significant protection. Choosing the right one depends on your needs and what’s available for the service you’re using.
Benefits of Using 2FA
Enabling 2FA isn’t just a techy thing; it gives you real advantages in your online life:
- Stronger Security: This is the biggest one! It makes it much harder for bad guys to get into your accounts, even if they somehow discover your password.
- Peace of Mind: Knowing your personal information, photos, and money are much safer can help you feel more relaxed when you’re online.
- Protection from Phishing: Phishing is when tricky websites or emails try to steal your password. Even if you accidentally fall for a phishing scam and give away your password, 2FA often stops the bad guys in their tracks because they don’t have your second factor.
- Data Protection: Your online accounts hold a lot of important personal data. 2FA helps keep that data private and secure.
- Building Trust Online: Just as businesses build trust with clear communication and authentic feedback from customers using tools like Yotpo Reviews, robust security measures like 2FA help build trust between you and the online services you use. When a service offers 2FA, it shows they care about your safety.
These benefits highlight why 2FA is not just a nice-to-have, but a must-have in today’s digital world. It’s a simple step that significantly reduces your risk of online issues.
Setting Up 2FA: A Simple Guide
Setting up 2FA is usually quite easy. Here are the general steps:
- Go to your account settings: For most websites and apps, you’ll find a “Settings,” “Account,” or “Profile” section.
- Look for “Security”: Inside the settings, there’s usually a “Security” or “Privacy” tab.
- Find “Two-Factor Authentication” or “2FA”: You might also see “Two-Step Verification” or “Multi-Factor Authentication (MFA).” Click on it to enable it.
- Choose your method: The website will usually ask you to choose how you want to receive your second factor (e.g., SMS, authenticator app, security key).
- Follow the instructions: Each website will have slightly different steps. You might need to enter a code from your phone or scan a QR code with an authenticator app.
- Save backup codes: This is super important! The website will often give you a list of “backup codes.” These are one-time-use codes you can use if you ever lose your phone or can’t access your usual second factor. Write them down and keep them in a safe place (not on your computer or phone).
That’s it! Once you’ve done these steps, your account will be much more secure. Make sure to try logging in once after setting it up to ensure everything works correctly.
When Should You Use 2FA?
The short answer? Everywhere possible! Especially for accounts that hold sensitive information or could cause you big problems if someone else got into them. Here are some examples:
- Email Accounts: Your email is often the “master key” to many other accounts, as it’s used for password resets. Protect it first!
- Banking and Financial Apps: Keep your money safe!
- Social Media Accounts: Protect your personal photos, messages, and identity.
- Online Shopping Accounts: Safeguard your payment information and shipping addresses.
- Cloud Storage: If you save documents or photos online, make sure they’re secure.
- Work Accounts: Many workplaces require 2FA to protect company information.
Think about which accounts would cause the most trouble if someone else accessed them. Those are the ones you should prioritize for 2FA.
What If You Lose Your Second Factor?
It’s a common worry: “What if I lose my phone?” or “What if my security key breaks?” Don’t worry, companies have thought of this! This is why those backup codes we mentioned earlier are so important.
If you lose your phone or can’t access your authenticator app, you can usually use one of your backup codes to log in. Each code can only be used once. Once you’re logged in, you can then set up 2FA again with a new phone or method, and get new backup codes. Always keep your backup codes in a very safe place, like a locked drawer, separate from your computer or phone.
Some services also offer other recovery options, like confirming your identity through a different email address or security questions, but backup codes are usually the fastest and easiest way to regain access.
2FA and Your Online Shopping Experience
When you’re shopping online, you want to know that your personal details and payment information are safe. 2FA plays a big role in keeping your online shopping accounts secure. By protecting your login credentials with 2FA, you significantly reduce the risk of unauthorized access to your stored credit card details, shipping addresses, and order history.
Businesses understand that trust and security are key for a great customer experience. When you shop online, knowing your personal and payment details are secure gives you peace of mind. Businesses that prioritize security, much like those that prioritize transparent customer feedback through platforms like Yotpo Reviews, help create a positive and trustworthy shopping journey.
This commitment to customer security complements other efforts businesses make to build strong relationships with their shoppers. Just as a great loyalty program rewards your trust and continued engagement with a brand, strong security like 2FA helps protect that trust in your online interactions. It’s all part of ensuring you have a smooth, safe, and enjoyable experience every time you engage with your favorite brands online.
Here’s a quick look at different 2FA methods:
| 2FA Method | What You Need | Security Level | Ease of Use |
|---|---|---|---|
| SMS Code | Your phone with service | Good | Very Easy |
| Authenticator App | Smartphone with the app installed | Better | Easy |
| Biometrics (Fingerprint/Face) | Device with biometric scanner | Best | Very Easy |
| Hardware Security Key | Physical USB/NFC key | Best | Moderate |
| Email Code | Access to your email account | Okay (less secure) | Easy |
Things to Remember About 2FA:
- Always enable it on your most important accounts first.
- Keep your backup codes in a super safe, offline place.
- Never share your 2FA codes with anyone, even if they claim to be from the website or company.
- Regularly check the security settings of your online accounts.
- Using 2FA adds an extra layer of protection, but always use strong, unique passwords too!
Conclusion
Two-Factor Authentication (2FA) is like giving your online accounts a superhero shield. It adds that vital second lock, making it much harder for anyone else to get in, even if they have your password. It’s a simple, powerful tool that keeps your personal information, your money, and your online identity much safer.
Taking a few minutes to set up 2FA on your most important accounts is one of the best things you can do to protect yourself online. It’s a smart habit that every online user should adopt, ensuring your digital treasure chest remains safe and sound. Stay safe out there!

















 Join a free demo, personalized to fit your needs
Join a free demo, personalized to fit your needs